What is OpenVPN, And How Does it Work?

Virtual Private Network, or a VPN, refers to a virtualized network that provides a secure method through which an internet-enabled device, say your personal computer, connects to a remote VPN server by encrypting data and cloaking the originating IP address so as to bypass blocks posed on websites and internet firewalls. Accordingly, you can use them to access restricted websites while maintaining your privacy.
OpenVPN is an open-source connection protocol that forms a safe tunnel between two network nodes. Many virtual private networks trust this technology to secure and encrypt every bit of information that flows over the Internet.
Below, we will provide a more detailed explanation of what the OpenVPN server is and when it is most effective. First, what is OpenVPN?
What is OpenVPN?
OpenVPN is open-source software that remotely combines software protocols, which will help create private and secure connections. This software enables remote access by ensuring an individual is bound to software protocols to establish private, safe connections.
OpenVPN is widely renowned for providing very strict security through the protocol's identity control via authentication with both digital certificates and user credentials. It applies a layer of secure communication protocols, including SSL/TLS, founded on a secure tunneling layer for data transfer.
This safeguards that every type of sensitive information, including personal data, financial details, or the communication involved in business, may be duly protected from access by unauthorised persons or even eavesdropping.
OpenVPN Protocols
UDP (User Datagram Protocol) and TCP (Transmission Control Protocol) are the primary protocols OpenVPN offers.
OpenVPN UDP highly prioritizes speed over dependability. It is appropriate for demanding tasks like VoIP conversations, gaming, and streaming. It results in speedier transmission but a weaker guarantee of packet delivery because it doesn't create a connection between sender and recipient.
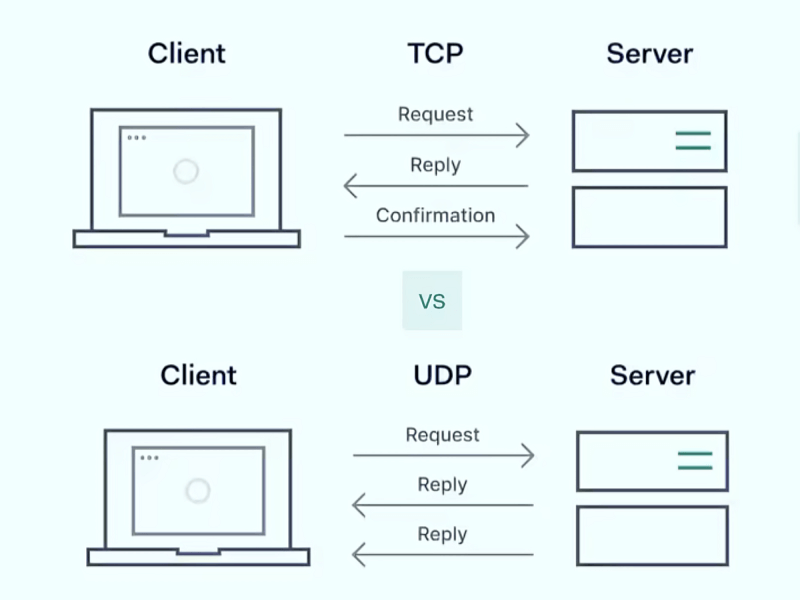
On the other hand, TCP strongly emphasises dependability by carefully verifying data packets while they are in transit and ensuring they arrive at their destination undamaged. Because of this, it is appropriate for static applications where data integrity is crucial, such as email, online browsing, and file transfers.
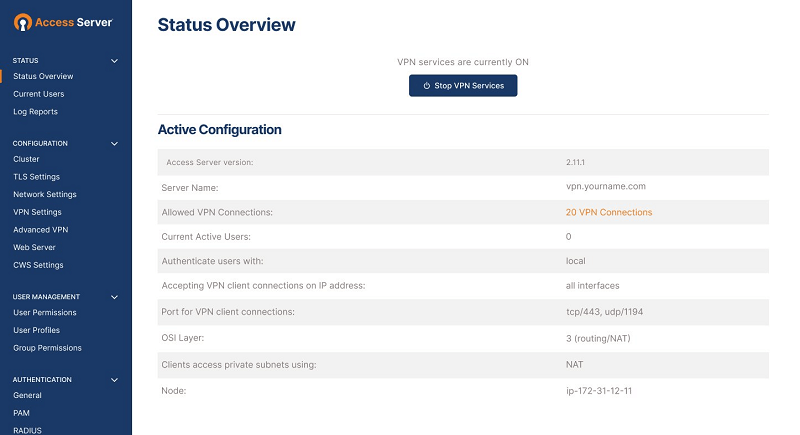
The particular use case determines two protocols: TCP and UDP ports. A TCP-specific port is recommended for applications where data sequencing and dependability are critical, but a UDP port is suggested for tasks demanding speed. By default, the access Server is set up with OpenVPN daemons running on ports like TCP port 443 and UDP port 1194.
How Does OpenVPN Server Work

OpenVPN can protect TCP and UDP traffic using various authentication and configuration techniques and encryption algorithms. It's a recommended and secure option for many VPN installations because of all the customisation.
Now that you have that out of the way, the following are the essential details regarding using the OpenVPN protocol:
1. Authentication
Several techniques are used to confirm the legitimacy of the VPN server and OpenVPN client. These techniques frequently use public key infrastructure (PKI), digital certificates, and user credentials, which allow only authorised users to establish a VPN connection.
2. Tunnel Formation:
After successful authentication, a secure OpenVPN tunnel is created between the VPN client and the server. The primary protocol that Secure Sockets Layer/Transport Layer Security (SSL/Tjson/) is used for in constructing a VPN is tunneling, where the communication is given out over an authenticated, encrypted channel.
3. Data Encapsulation and Encryption
Data encapsulation encases data packets in extra safety and routing information layers. This procedure protects and keeps data intact while transmitting across VPN tunnels.
The encryption offers extra protection by encrypting the encapsulated data and rendering it unreadable to unauthorised parties. Data protection can be improved by configuring different encryption methods and critical lengths based on requirements.
4. Data Transmission
Traffic containing encrypted data travels to the VPN server via the established VPN tunnel. The data is decrypted and sent to its intended location at the server end. Thanks to the encryption, sensitive data is shielded from unauthorised access during transmission.
5. IP Addresses Concealment Through VPN server
Since communication goes via a middle VPN server, OpenVPN hides the IP address of the source and only displays the VPN server's IP address to the destination. This function improves anonymity and privacy by concealing IP addresses and stopping outside parties from seeing or following users' online activities.

Pros and Cons of OpenVPN
Benefits of OpenVPN
Versatility and Adaptability: OpenVPN is appropriate for several use cases due to its extreme versatility and ability to adjust to diverse network setups. It enables variable deployment options based on organisational demands by supporting client-servers and site-to-site connectivity.
Robust Security Features: It provides strong security measures, guaranteeing the privacy of any data transferred over the VPN. These features include encryption techniques like AES 256-bit and ChaCha.
Regular Updates: The open-source community drives frequent upgrades and enhancements that keep the protocol up to speed with emerging operations and technologies.
Ability to Bypass Firewalls: OpenVPN is useful for getting around any firewall and other restrictive network regulations because of its flexibility with TCP and UDP protocols, particularly when set to use TCP Port number 443.
Wide Platform Support: It is compatible with a wide range of routers and devices and major operating systems like Linux, Windows, Android, and iOS.
Cost-Effective Solution: The tool is affordable for people and businesses seeking a safe VPN server without paying high licensing costs to configure because it is available as an open-source portable app.
Disadvantages of OpenVPN
Potential Speed Limitations: Compared to other VPN protocols like WireGuard, OpenVPN may cause slower connection rates, depending on the encryption settings and network conditions.
Complex Installation Process: Its manual installation and configuration can be difficult and time-consuming, requiring technical know-how and an understanding of networking principles.
Server Compatibility Challenges: It is not pre-installed on systems, in contrast to specific VPN protocols integrated into particular platforms or gadgets. To use OpenVPN, users might need to install third-party VPN clients or software, which would require an additional step in the setup procedure.
Potential Blocking by Networks: Because of its widespread use and identifiable traffic patterns, censorship or network administrators may target OpenVPN, which could block connections.
Potential Security Risks: Setting up multiple OpenVPN instances may present various safety issues, such as exposing sensitive information to foreign attackers.
Comparing OpenVPN with other VPN Protocols
All VPN protocols have unique benefits and limitations. Let's examine them to see how OpenVPN differs from the others.
OpenVPN vs. WireGuard
As a well-established protocol, OpenVPN provides strong safety measures and customisable choices. It also provides good data protection, as it uses OpenSSL libraries and supports several encryption techniques, including AES 256-bit encryption.
Conversely, WireGuard is praised for its modern design, straightforward use, efficiency and the fact that it is easily configured. It uses fewer resources and has a lighter codebase with simplified cryptographic primitives. A well-recognized VPN provider, Nord VPN, uses Wireguard.
In contrast to OpenVPN, which has undergone rigorous testing over the years, WireGuard is very new despite its advantages. For business or security-sensitive applications in particular, customers tend to favour OpenVPN's versatility and track record over WireGuard's simplicity, as it addresses their requirements.
OpenVPN vs. IKEv2/IPsec
Two popular VPN protocols with different features are OpenVPN and IKEv2/IPsec. Due to OpenVPN's open-source nature and many adjustable options, customers may customise network setups and encryption techniques to suit their requirements.
It offers flexibility in balancing safety and performance needs because of its compatibility with TCP and UDP ports.
On the other hand, mobile devices and migrating networks favour IKEv2/IPsec because of its reliable security and easy communication. Thanks to IPsec's robust authentication and encryption protocols and IKEv2's automatic reconnection features, data is continuously protected even in the event of network outages or device changes.
OpenVPN is still a flexible and dependable choice for various networking scenarios, even while IKEv2/IPsec shines in certain use cases like mobile VPNs and site-to-site connections.
OpenVPN vs. SSTP
Both of the above VPN protocols differ greatly in terms of capabilities and applications. OpenVPN is extremely customisable and open-source, so it is extensively used on a variety of systems and excels in adaptability.
However, Microsoft's SSTP (Secure Socket Tunnelling Protocol) is an excellent option for environments primarily using Windows since it connects with Windows systems without any issues. It prioritises protocol stability and usability, and because it relies on SSL/TLS encryption, it can navigate network proxies and firewalls with effectiveness.
Platform compatibility, network constraints, and deployment preferences are major factors influencing the decision between OpenVPN and SSTP.
Why Choose OpenVPN?
OpenVPN is a top option for protecting your online activity for various reasons. However, having a specific parameter while choosing this tool over others would be best.
Above all, the OpenVPN server uses advanced encryption techniques like AES 256-bit encryption. It supports Perfect Forward Secrecy (PFS), which improves data privacy by creating distinct encryption keys for every session.
Furthermore, the fact that it is open-source encourages ongoing evaluation and development by a worldwide community of programmers and security specialists. By working together, vulnerabilities are found and fixed quickly, preserving the integrity and dependability of the protocol.
It offers unparalleled adaptability by enabling users to alter network setups, authentication procedures, and encryption settings to suit their requirements. This degree of personalization improves safety while also optimizing performance according to user preferences.
In terms of accessibility, it guarantees compatibility with most devices by supporting a broad range of platforms, such as Windows, macOS, Linux, Android, and iOS. Its choices for TCP and UDP ports also show its adaptability to various use cases and network situations.
Finally, its affordability contributes to its allure. It is available as part of many reliable VPN services, frequently at cheap pricing, and the protocol is free.
VPSServer and OpenVPN
VPS server is a platform widely known for hosting websites, applications and services. Because of root access, VPS hosting enables you to have unmatched control over your virtual server space. You may personalise your virtual space with your VPS Hosting plan.
OpenVPN is frequently installed on VPS servers to provide safe and private connections for users who want to access the server. It offers strong encryption and versatility, making it a top choice for enterprises and users.
Frequently Asked Questions
What are OpenVPN Daemons and Multiple OpenVPN Daemons?
OpenVPN daemons are the background apps that oversee operations. By running multiple OpenVPN daemons concurrently, one OpenVPN daemon may manage several VPN connections. For example, "Openvpn" is used for the primary service, and "openvpn-serv" is used for server configuration.
How do I Configure my own VPN OpenVPN?
The first step to configure OpenVPN is to install the programme and make a configuration file. Edit the configuration file to specify user authentication, server configurations, and encryption techniques. Launch the OpenVPN service when configured to create secure connections between clients and the server.
What is port forwarding, and what use does port forwarding have?
One of the networking techniques forwarded from the outside to a certain device or service includes port forwarding. Port forwarding routes incoming data packets from a specific router port to a port of choice on a device, letting it access network-hosted services, such as web and gaming servers.
What are the benefits of port forwarding?
Port forwarding has various advantages, including remote access to network services like web and game servers. Furthermore, port forwarding improves safety by routing traffic through certain ports and enabling effective communication between internal and external devices.
How can I connect a VPN Client Device to an Access Server?
The following steps should be followed while connecting clients to an Access Server:
-
Install the client software on your device.
-
Launch the software and import the Access Server configuration file.
-
Fill in the login information provided by the Access Server administrator.
-
Connect to the Access Server to set up a secure VPN connection.











